This website is designed to be informational, please support by commenting or emailing me on the contact form more scams you know about.

When identifying potential scams, recognizing common scam scripts and red flags is crucial to safeguard oneself against fraudulent schemes. Here’s an overview of some common types of scams, their typical scripts, and key indicators that you might be dealing with a scam:
 These scams typically involve impersonating a legitimate organization to trick individuals into revealing sensitive information. AI can analyze the email content and identify suspicious patterns, such as misspellings, generic greetings, or requests for personal information. Here is a sample:
These scams typically involve impersonating a legitimate organization to trick individuals into revealing sensitive information. AI can analyze the email content and identify suspicious patterns, such as misspellings, generic greetings, or requests for personal information. Here is a sample:
“Dear Customer,
We have noticed some unusual activity on your account. Please click on the link below to verify your account details. Failure to do so may result in the suspension of your account.
[Link]
Thank you,
Customer Support”
AI-generated tags: #phishing #suspiciouslink

In recent years, the rise of bank fraud scams has left many individuals vulnerable to significant financial losses. Scammers use a variety of tactics to trick people into divulging personal information or transferring money under false pretenses. Unfortunately, banks often claim that they are not liable for these scams, stating that the incidents are not classified as fraud but rather as scams.
This distinction can be confusing for customers, as the end result is the same: their money is stolen. Banks like Chase have been notable examples where customers have reported difficulty in getting their money back after falling victim to scams. The lack of accountability from these financial institutions leaves many feeling unprotected and frustrated.
To combat this issue, it is crucial for banks to take a more proactive stance in protecting their customers. This includes:
By taking these steps, banks can help reduce the incidence of scams and build greater trust with their customers. Financial institutions have the resources and capabilities to make a significant impact in the fight against scams, and it is their duty to use these assets to protect the public.

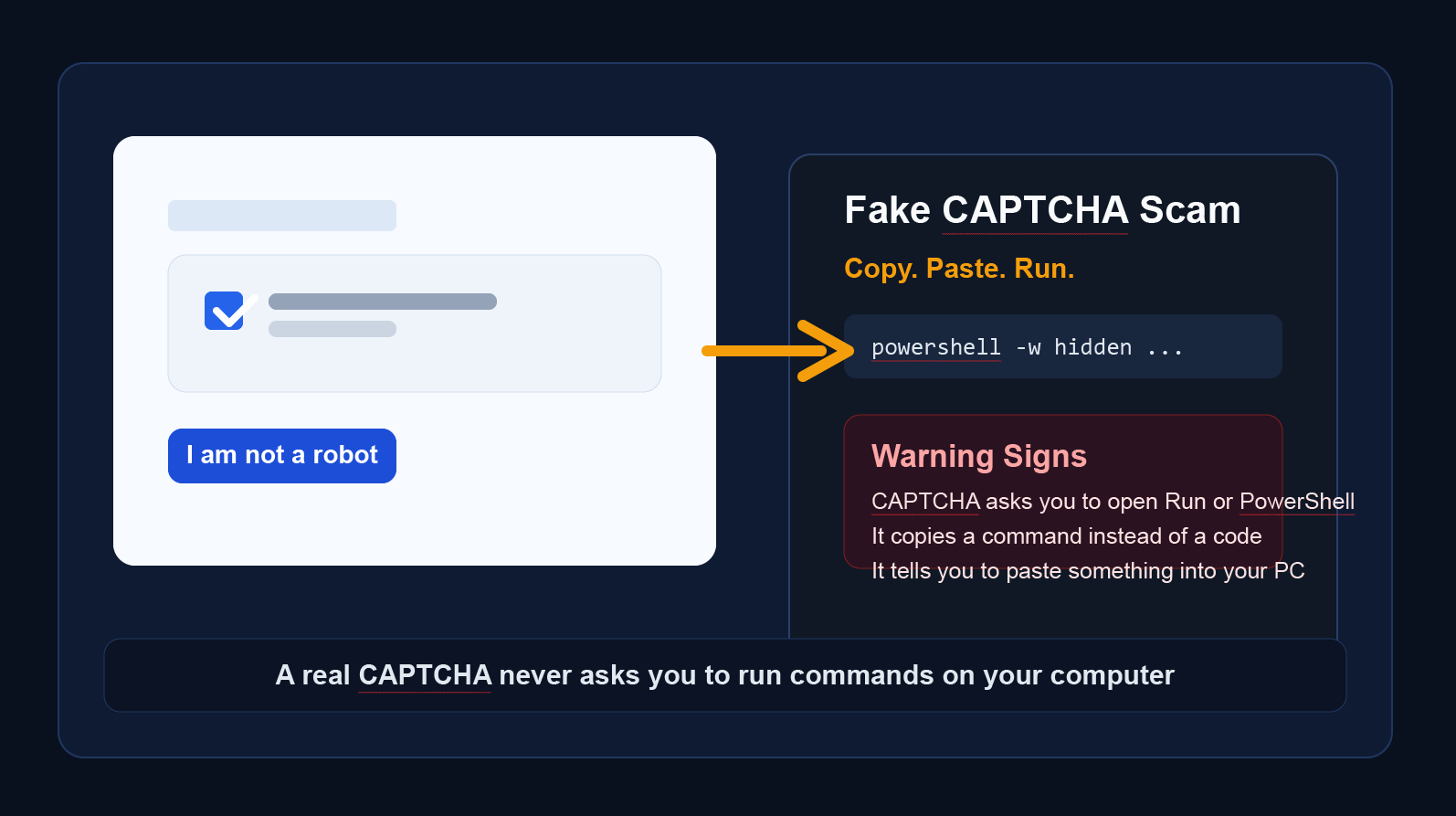
In tech support scams, fraudsters pose as tech support representatives to gain remote access to a victim’s computer or extract payment for fake services. AI can analyze phone conversations or chat transcripts and flag phrases like:
– “Your computer has been infected with a virus! We can fix it for you.”
– “Please provide your credit card details to proceed with the payment.”
AI-generated tags: #techsupportscam #fakevirusalert

Empathy spams, often referred to as “empathy scams,” are tactics used by malicious individuals to exploit others’ emotions for personal gain. These scams typically involve creating a false narrative or situation to evoke sympathy, compassion, or concern from the target. Common examples include fake charity requests, fabricated sob stories, or impersonating someone in distress. The goal is to manipulate the target into providing money, personal information, or other forms of support.
Here are some key characteristics of empathy spams:
To avoid falling victim to empathy scams, it’s important to verify the authenticity of any distressing claims, donate through reputable channels, and be cautious about sharing personal information.
Tags: #Empathyscam
 Imposter scams involve fraudsters pretending to be someone they’re not to steal money, personal information, or both. One common variant is when scammers pose as representatives from utility companies. Here’s how these scams typically unfold:
Imposter scams involve fraudsters pretending to be someone they’re not to steal money, personal information, or both. One common variant is when scammers pose as representatives from utility companies. Here’s how these scams typically unfold:
Initial Contact: The scammer contacts the victim, claiming to be from their utility company, such as electricity, water, or gas service. This contact may be via phone call, email, or even a home visit.
Urgent Demand: The scammer informs the victim that their utility bill is overdue, and their service will be disconnected imminently unless they make an immediate payment.
Request for Payment: Victims are instructed to pay using specific methods that are typically untraceable and irreversible, such as prepaid debit cards, gift cards, or wire transfers.
Pressure Tactics: Scammers apply pressure by insisting on the urgency of the situation, often claiming that the disconnection will occur within hours if the payment is not made.
Immediate Threats: Legitimate utility companies usually provide multiple overdue notices before disconnection and will not demand immediate payment over the phone or via email.
Payment Method: Be suspicious if you’re asked to pay your utility bill using prepaid debit cards, gift cards, or wire transfers. Utilities generally offer a variety of standard payment options, including checks, credit cards, and online payments.
Caller ID Deception: Scammers can spoof caller ID to make it appear as though the call is coming from your utility company. If in doubt, hang up and call the customer service number listed on your utility bill.
Verification: Verify any claims by contacting your utility provider directly using the number on your bill or their official website, not the contact information provided by the caller or email sender.
Do Not Provide Personal Information: Never give out personal or financial information over the phone to unsolicited callers.
Educate Yourself: Be aware of the tactics used in these scams and educate family members, especially those who might be more vulnerable.
Report the Scam: If you suspect a scam, report it to your utility company and local authorities. This can help prevent others from becoming victims.
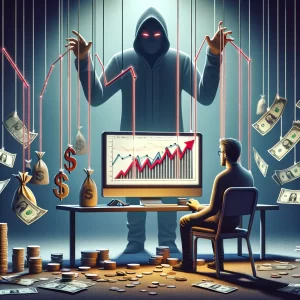 These scams promise high returns on investments but are designed to swindle money from unsuspecting individuals. AI can analyze investment offers and identify red flags, such as:
These scams promise high returns on investments but are designed to swindle money from unsuspecting individuals. AI can analyze investment offers and identify red flags, such as:
– Guaranteed returns with no risk
– Pressure to invest quickly
– Lack of transparency or vague explanations
 “Dear Customer,
“Dear Customer,
We are pleased to inform you that you have been selected as a lucky winner of our exclusive online shopping promotion! You have won a brand new iPhone X worth $1000!
To claim your prize, please click on the link below and enter your personal information, including your name, address, and credit card details. Hurry, as this offer is only valid for the next 24 hours!
Click here to claim your prize: [Scam Link]
They may say “time-sensitive, and failure to claim your prize within the specified time will result in the forfeiture of your winnings.”
– Remember, it’s crucial to be vigilant and skeptical when encountering such messages, and to verify the authenticity of any promotional offers before providing any personal information or clicking on suspicious links.
 Gig or commission scams target freelancers, artists, and other professionals looking for work or opportunities to sell their services. These scams can take various forms but typically involve tricking individuals into providing work, services, or money upfront with the false promise of payment or commission later on. Here’s how these scams usually operate and some common variations:
Gig or commission scams target freelancers, artists, and other professionals looking for work or opportunities to sell their services. These scams can take various forms but typically involve tricking individuals into providing work, services, or money upfront with the false promise of payment or commission later on. Here’s how these scams usually operate and some common variations:
Initial Contact: Scammers pose as potential clients, reaching out to freelancers or artists with a job offer. This can happen via email, social media platforms, freelance job boards, or through the professional’s website.
The Offer: The scammer presents a seemingly lucrative offer or commission that is often too good to refuse. It could involve a large project, a high-profile client, or a significant amount of money.
The Catch: Once the professional shows interest, the scammer introduces a catch. This might involve the professional needing to pay a fee upfront (for materials, software, training, or security deposits), submit personal information, or complete work as a “test” before being officially hired.
Payment Issues: If the professional completes the work, they may be presented with fake payment proofs, checks that bounce, or continuous excuses about payment delays. In some cases, the scammer disappears once the work or payment for supposed fees has been submitted.
Advance Fee Fraud: The freelancer is asked to pay an upfront fee for “administration,” “materials,” or “software licenses” before they can start work or receive the project details.
Overpayment Scam: The scammer “accidentally” sends a check for more than the agreed amount, then asks the freelancer to refund the difference. Later, the original check bounces, leaving the freelancer out of pocket.
Phishing Attempts: Under the guise of setting up a direct deposit or payment, the scammer asks for personal and banking information, leading to identity theft or unauthorized access to the freelancer’s accounts.
Fake Contests: Artists are invited to participate in contests with entry fees, promising exposure or prizes that never materialize.
Verify the Client: Research the client or company offering the gig. Look for reviews, testimonials, or any red flags online.
Never Pay Upfront Fees: Legitimate clients and job offers will not require you to pay money upfront to start working or receive payment.
Use Trusted Platforms: Work through reputable freelance platforms that offer payment protection and vet clients.
Secure Payment Methods: Request payment through secure, traceable methods and agree on a payment schedule before starting work.
Be Skeptical: If an offer seems too good to be true, it probably is. Trust your instincts and proceed with caution.
By being vigilant and adopting these strategies, freelancers and artists can protect themselves against gig and commission scams.
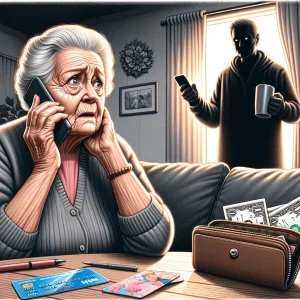 The Grandparent Scam is a type of fraud that preys on the emotions of elderly individuals by exploiting their love and concern for their grandchildren. This scam typically unfolds as follows:
The Grandparent Scam is a type of fraud that preys on the emotions of elderly individuals by exploiting their love and concern for their grandchildren. This scam typically unfolds as follows:
Initial Contact: The scammer calls the victim, posing as a grandchild in distress or someone representing them (such as a lawyer or law enforcement officer). They often start the conversation with a phrase like, “Hi Grandma/Grandpa, do you know who this is?” This prompts the victim to guess the name of the grandchild the scammer is pretending to be.
Creating Urgency: Once the scammer has established a false identity, they tell a convincing story designed to create urgency and panic. Common scenarios include claiming they have been arrested, involved in an accident, hospitalized, or stranded in a foreign country, and they urgently need money for bail, medical expenses, or travel costs.
Requesting Secrecy: The scammer pleads with the victim not to tell anyone else in the family about the situation, claiming it would only make things worse or that they are too embarrassed. This isolates the victim and prevents them from verifying the story.
Demanding Money: The scammer instructs the victim to send money immediately, often through a wire transfer, gift cards, or other untraceable methods. They may provide specific instructions on how to send the funds to ensure it reaches them without detection.
Educating oneself and vulnerable family members about the existence and characteristics of the Grandparent Scam is crucial for prevention. Awareness is a powerful tool in combating this emotionally manipulative fraud.
 Impersonation scams have evolved significantly with the advent of artificial intelligence (AI), making them more sophisticated and harder to detect. AI technologies, including deepfakes and voice synthesis, enable scammers to impersonate individuals more convincingly, leading to a variety of frauds that can deceive even the cautious.
Impersonation scams have evolved significantly with the advent of artificial intelligence (AI), making them more sophisticated and harder to detect. AI technologies, including deepfakes and voice synthesis, enable scammers to impersonate individuals more convincingly, leading to a variety of frauds that can deceive even the cautious.
The key to protecting yourself against AI-driven impersonation scams is vigilance, verification, and staying informed about technological advancements. As AI technologies become more sophisticated, so too must our strategies for detecting and preventing fraud.
 A timeshare resale scam targets owners of timeshare properties who are looking to sell their shares. These scams can take various forms, but they typically follow a similar pattern designed to exploit sellers eager to offload their timeshares. Here’s how these scams generally work:
A timeshare resale scam targets owners of timeshare properties who are looking to sell their shares. These scams can take various forms, but they typically follow a similar pattern designed to exploit sellers eager to offload their timeshares. Here’s how these scams generally work:
Initial Contact: The scammer, posing as a broker or a company specializing in timeshare sales, contacts the timeshare owner or advertises services promising to help sell the timeshare quickly. Sometimes, the scammer claims to have a buyer already interested.
Upfront Fee Request: The scammer claims that to proceed with the sale, the owner must pay an upfront fee. This fee is allegedly for various services such as advertising, listing, or closing costs. The scammer assures the owner that this fee will lead to a quick sale.
High Pressure Sales Tactics: The scammer uses high-pressure tactics to convince the timeshare owner to pay the fee as soon as possible, often claiming that the interested buyer might walk away or that this opportunity is a one-time offer.
Disappearance or Continued Fees: Once the fee is paid, the scammer may disappear, or they might ask for additional fees for further “services” or “unexpected costs.” In many cases, the promised sale never materializes, and the owner is left with less money and still in possession of the timeshare.
Request for Upfront Fees: Legitimate timeshare resale services typically do not require large upfront fees. Instead, they might take a commission after the sale is completed.
Unsolicited Offers: Be cautious if you’re contacted out of the blue by someone claiming to have an immediate buyer for your timeshare.
Guarantees of a Quick Sale: Promises of a quick sale, especially at a high price, should be treated with skepticism.
High Pressure Tactics: Scammers often create a sense of urgency to push their targets into paying fees before they can thoroughly investigate the offer.
Research the Company: Look for reviews, complaints, and any information about the company online. Check if they are registered with the Better Business Bureau or any relevant regulatory bodies.
Never Pay Upfront Fees: Avoid companies that require you to pay fees before the sale is completed. Understand all terms and conditions before agreeing to any services.
Verify Claims: Independently verify any claims made by the resale company, especially if they say they have a buyer lined up.
Consult a Professional: Consider consulting a real estate attorney or a professional with experience in timeshare sales to review any contracts or agreements.
Timeshare resale scams can be sophisticated and convincing, but by being cautious and conducting thorough research, you can avoid falling victim to these fraudulent schemes.